Click fraud is a massive problem
An estimated $100 billion will be lost to ad fraud in 2023. That’s nearly 20 percent of all digital ad spend. Fraud Blocker solves this issue for marketers with advanced software that automatically blocks traffic from bots and other malicious sources.
22% of ad spend is lost to fraud
An in-depth study by independent research firm Juniper Research analyzed over 78,000 datasets and found 22% of all ad spend is lost to fraud.
Read the report (no email needed) →22% of ad spend is lost to fraud
An in-depth study by independent research firm Juniper Research found 22% of all ad spend is lost to fraud.
Types of Click Fraud We Detect
Types of Click Fraud
We Detect
Our platform detects some of the most popular and sophisticated fraudulent click activity used today.
Bots
Complex bots can inject malware onto a suspect’s computer which repeatedly clicks on your ads in the background.

Click Farms
Click farms hire workers to click on your ads all day using techniques that appear as if they’re coming from different users.

Competitors
Don’t think competitors are clicking on your ads? Think again. It’s an easy way for them to drain your ad budgets.

Malicious Publishers
Publishers can load their pages with ads that users never see such as inside a 1×1 iframe or stacking them on one another.
Accidental Clicks
Mobile often place ads in places where people click the most, thus driving up accidental clicks without any real intent.
Vengeful Customers
Unhappy customers will leave you bad reviews and click on your ads. Stop showing ads to them today.
Advanced Features That Protect Your Campaigns
Advanced Features
That Protect
Your Campaigns
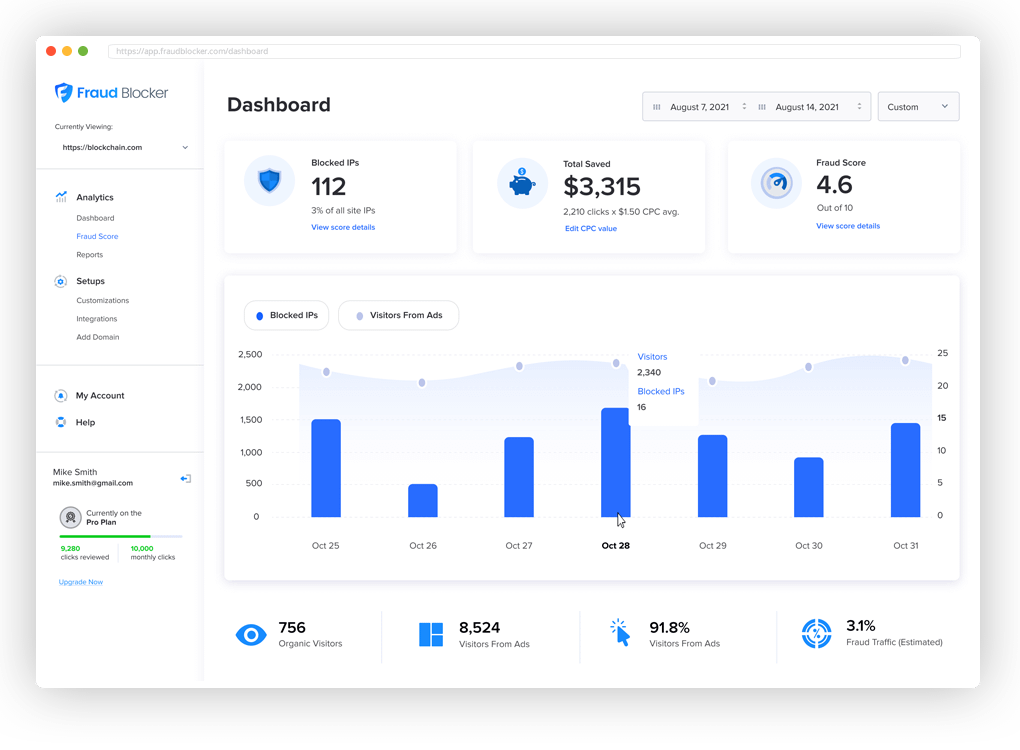
Our industry-leading service is able to detect fraudulent ad clicks to your website and then block them from displaying in near real-time. Reach more qualified users and generate more leads with our proprietary platform.

24/7 fraud monitoring

Click analysis and scoring

Real-time
email alerts

Customizable blocking rules

Real-time email alerts

Automated reporting

Exportable IP Addresses
How it Works
01
02
03
04
01
Easily place our fraud detection pixel on your website
02

Connect your
Google Ads account
with one click
03

We analyze your web traffic for fraud
04

We prevent ads from displaying on fraudulent sources
Why We’re Better

We're proudly based in the US
Fraud Blocker is fully developed in the United States by a team of former marketing executives.

We provide a network effect
Fraudulent sources on other sites within our network can be excluded from your site.

We offer a risk-free, 7-day trial
Our 7-day free trial is a great way to test our performance for your campaigns. Try us for free, with no contracts and flexible month-to-month plans.
Real Customers. Real Results.

Websites protected by Fraud Blocker



Fraud Blocker saved me $200 on $4,000 ad spend
Abder-KINANE
AppSumo Member
Incredible software that I love on day one
I am incredibly pleased with my purchase. If you work in paid media, this is a great piece of software at an incredible price. If you need someone to test features, let me know. Thanks again! Great software!
jnathangarrett
AppSumo Member
Very powerful and effective
Pallavi R.
Engineer
Pays for itself and stellar customer service
Business owner
Very clean with tons of potential
I was able to very quickly set up my Google Ads account and connect it right away. I input the average CPC and away we went. While the traffic is low on my current campaign, the data being pulled in once I put the pixel on the website appears to be accurate.
CWD1979
AppSumo Member
Great product!
Okay I just jumped onto an unlimited plan. All went smoothly and I was able to roll over all of my accounts from a Google Ads MCC account. If you’re authorizing through an MCC account the process is smooth and segregated with a clear separation between all of the sub accounts. Everything is great so far.
Rich77ard
AppSumo Member
Reviews
Real Customers.Real Results
Fraud Blocker saved me $200 on $4,000 ad spend
I manage Google Ads campaigns in France. It’s a good start and my client is very happy with the results because he suspected many fraudulent clicks and it turned out to be correct. I really recommend this app.
Abder-KINANE
AppSumo Member
Very powerful & effective
Pallavi R.
Engineer
Incredible software that I love on day one
Works With Any Website